

Recall is also not supposed to collect data from private sessions from popular web browsers.
it makes one wonder how well that works; if it’s based on OCR, does it “redact” the bounding box corresponding to the private window? What happens with overlapping windows; how does it handle windows with transparency; I can’t help to think there’s a high probability their solution is flaky.








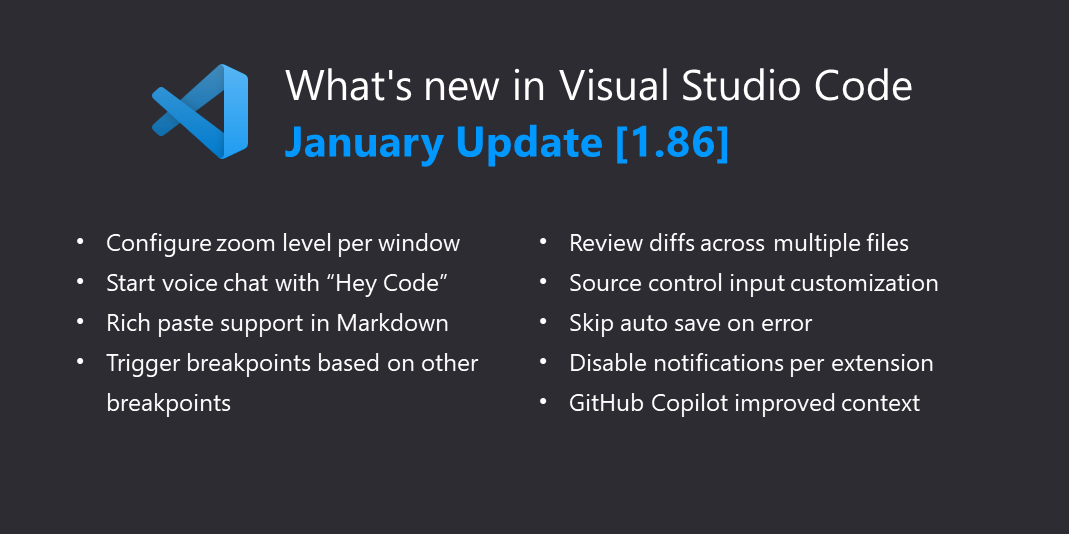
lol they barely changed anything visually